Stimuleert photoshoppen donatiegedrag?
Als mensen een foto zien van een schattige panda zijn ze eerder geneigd geld te doneren dan wanneer ze een afbeelding van een tarantula onder ogen krijgen. Dat is nu eenmaal het trieste lot van dieren die wat minder knuffelbaar zijn. Het al vele jaren bekende effect blijkt nu zó sterk dat mensen zelfs meer geld geven als ze een foto zien die overduidelijk bewerkt is om een schattig dier nog schattiger te laten ogen.
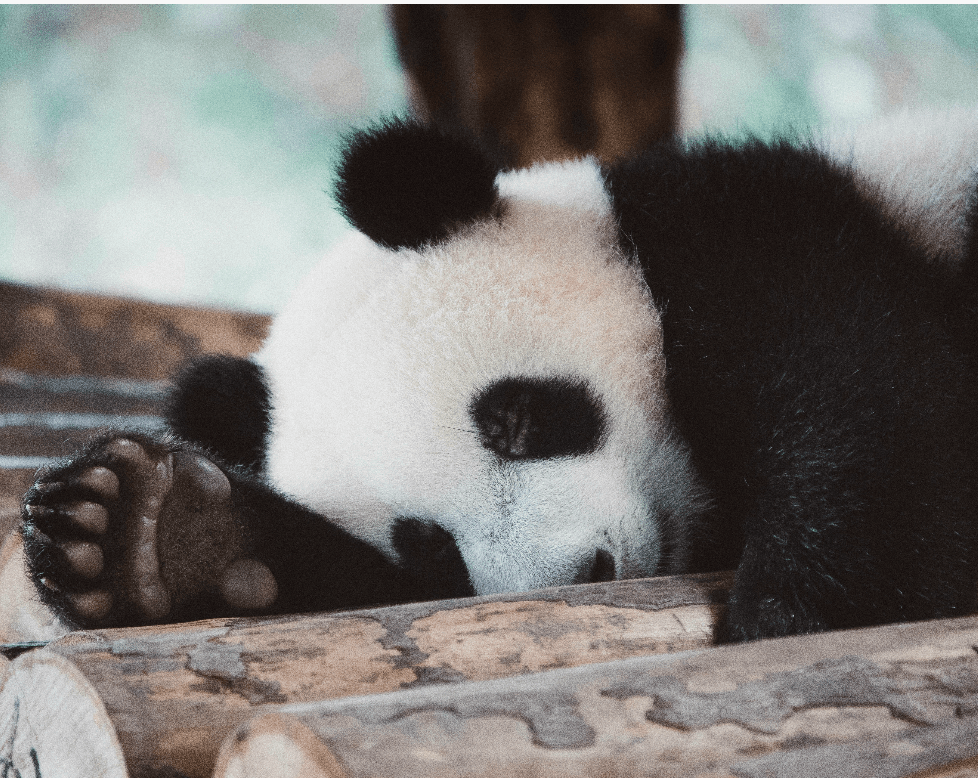
Onderzoekers van Deakin University (Australië) en Oxford University (VK) toonden groepen proefpersonen foto’s van verschillende dieren. De beelden waren in verschillende mate bewerkt. Deelnemers moesten een hypothetisch geldbedrag verdelen over de dieren. Wat bleek? Dieren wier foto overduidelijk was gephotoshopped zodat ze er schattiger uitzagen (aaibaarder, grote ogen, geen scherpe tanden) brachten duidelijk het meeste geld in het laatje. Tenminste, bij de groep deelnemers die uit het algemene publiek was geworven. Een groep natuurbeschermers die ook meedeed aan de studie had juist een afkeer van de verschattigde foto’s en koos voor de onbewerkte beelden.
Minder giften via smartphone
Mensen die geld doneren via hun smartphone zijn minder vrijgevig dan mensen die een goed doel steunen op een computer. Dat blijkt uit een studie van de University of Connecticut (VS). Wie met zijn telefoontje bezig is, is meer op zichzelf gericht. Dat gaat minder goed samen met de empathie en het altruïsme dat komt kijken bij het doneren van geld.
In een eerste studie vroegen de onderzoekers 232 proefpersonen om een enquête in te vullen. Het kleine geldbedrag dat ze ermee verdienden mochten ze óf doneren aan het Rode Kruis óf zelf houden. Wat bleek? Van de deelnemers die de enquête op

Barrières weg voor fondsen om te investeren
Volgens de Vereniging van Fondsen in Nederland (FIN) creëert het Ministerie van Financiën met de publicatie van criteria voor algemeen nut helderheid en een gelijk speelveld. Aldus een uitgebreid persbericht. Tegelijk zwelt in de sector Filantropie de roep aan om scherper toezicht op de circa 45.000 Algemeen Nut Beogende Instellingen (ANBI's).

 nl
nl











